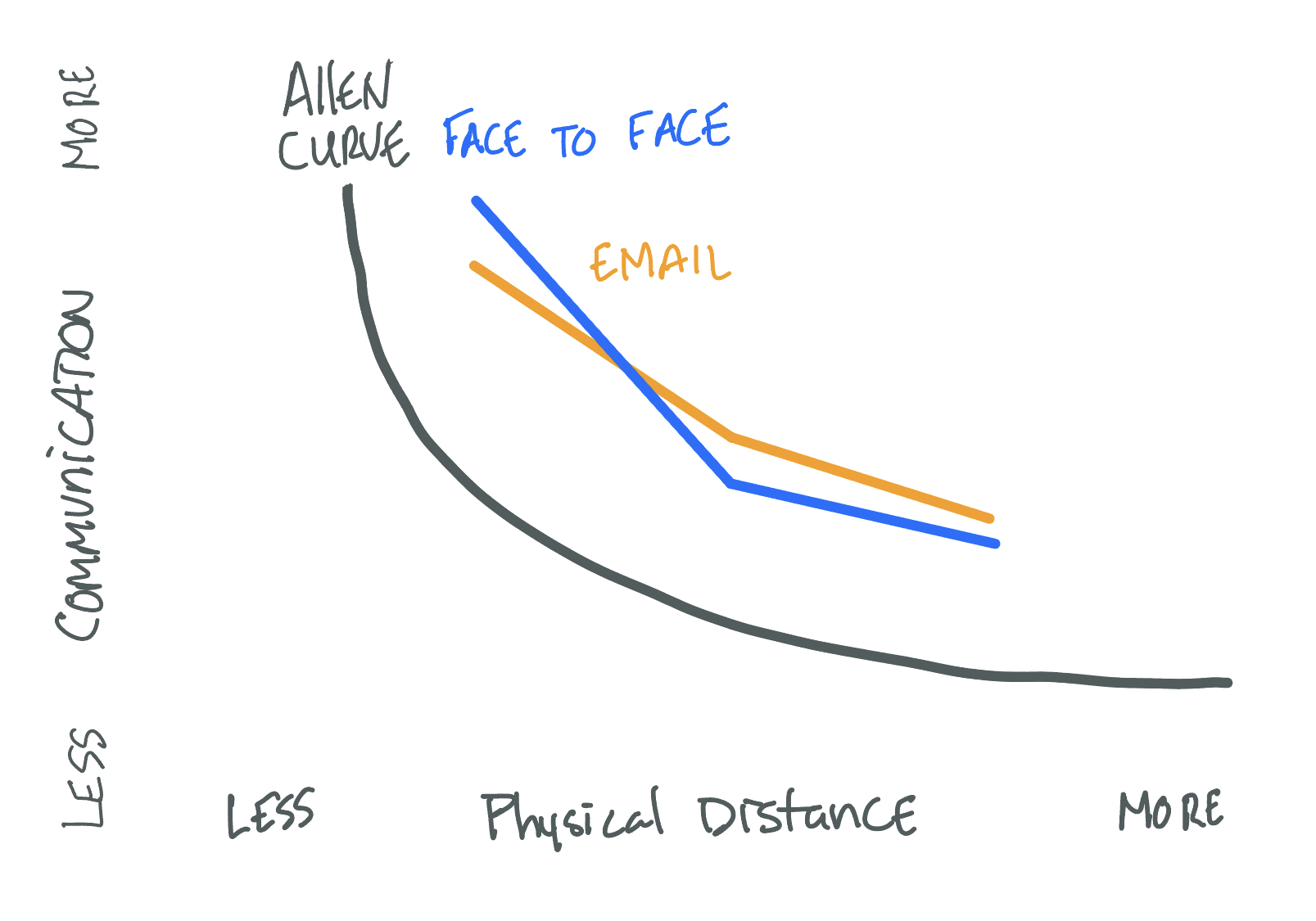
I’m surprised at how many people are not familiar with this idea. Regardless, as distance increase communication decreases. It makes sense. When you were in school you stayed in contact with your classmates more often. As people moved the communication between people became less frequent. You may have experienced this during the pandemic with coworkers. The person you got coffee with every morning and chatted about work or real world events you no longer communicate with on a regular basis. I’ve seen this apply with people just switching floors or moving to a different part of the building. The distance doesn’t need to be far for communication to drastically decrease.
If you are back in the office walking around can be a good way to stay in touch, as well as get a little exercise and a break from the computer. Working remotely is tougher. That’s why I set up reminders to connect with people every so often. This can be a week, month, months, or several months.
Reciprocity
Give without expecting something in return. First, this is a great feeling to just give without expecting something in return. Letting go of the return also helps with any frustration or anger that might occur from not getting something back. This can feel difficult because we all would like to think people will return the favor but it is something that can be practiced. Most people will want to return the favor. It might not be immediate but it will come at some point. Some people won’t return the favor. Either way we learn something about that person. Be careful to identify what people consider a favor because we’ll all have different ideas.
The five love languages is a great resource to read and understand. Some people just want help with their work. Others will want gifts or money compensation. Others will want praise. Understanding what drives people will help better understand what they may give in return.
I enjoy helping others and would rather someone help me than give me a gift. I would often look into help desk tickets for others and try to push them along if I could. This was a small effort for me but paid off when I needed something from these same people. Often, because I had helped them they would return the favor.
Be yourself
Be genuine and authentic. People can tell if you’re just there to get something out of them. If someone determines another person has or is trying to manipulate them the relationship is toast. Be who you are and don’t try to be someone else. You can work to make positive changes in your behavior and habits but ultimately we’re all who we are. I’ve struggled with being myself. I want everyone to like me but that just isn’t possible. I’ve tried being someone else for people and it doesn’t work. I have improved how I interact with people but ultimately I have to still be true to myself and accept that I won’t connect with everyone.
Easy to start habits
Two techniques I like to tell people to start with is using people’s name and saying thank you. Again, people are their favorite subject and hearing there name is a good feeling. You’ll have to identify what and how people liked to be called. Don’t just shorten people’s names because some people like being called by their first name. Some people like using their middle name or nickname. It is also a great way to start a conversation.
Say, “Thank you!” This is so easy to do and one of the least used techniques in the workplace. Say thank you to people for their work. Say thank you for getting you something. Say thank you for sharing their insights. It’s so easy to do and something people don’t hear enough.
Summary
Relationships are a very powerful thing. They can help advance a career and they can help get a job. To build a strong relationship, make it about the other person. Ask questions and spend time with them. Give without expecting something in return. This can feel very difficult because we are very transactional and want to get what’s rightfully ours. Most people will return the favor. The ones that don’t you will still learning something about them.
Finally, Be yourself and start small. Be who you are but realize you can make improvements to your behavior and habits. One of those can be by using people’s name and saying “Thank you!” for something they’ve done. Gratitude is a powerful thing and makes you and the other person feel good.
How do you go about building good relationships with people? Leave a comment below.
Resources
If you want to learn more about social engineering check out my GitHub page, Social Engineering for the Blue Team. You can also click on Social Engineering page or reach out to me directly with any questions you may have.