I recently gave this talk at BSides Augusta and DerbyCon this past September. BSides Augusta is a longer version where I demonstrate each tool. DerbyCon is a shorter version where I talk about each tool. After presenting at IT-ology Trends 2015, I decided to document the talk here on my site as a reference for people interested in the content.
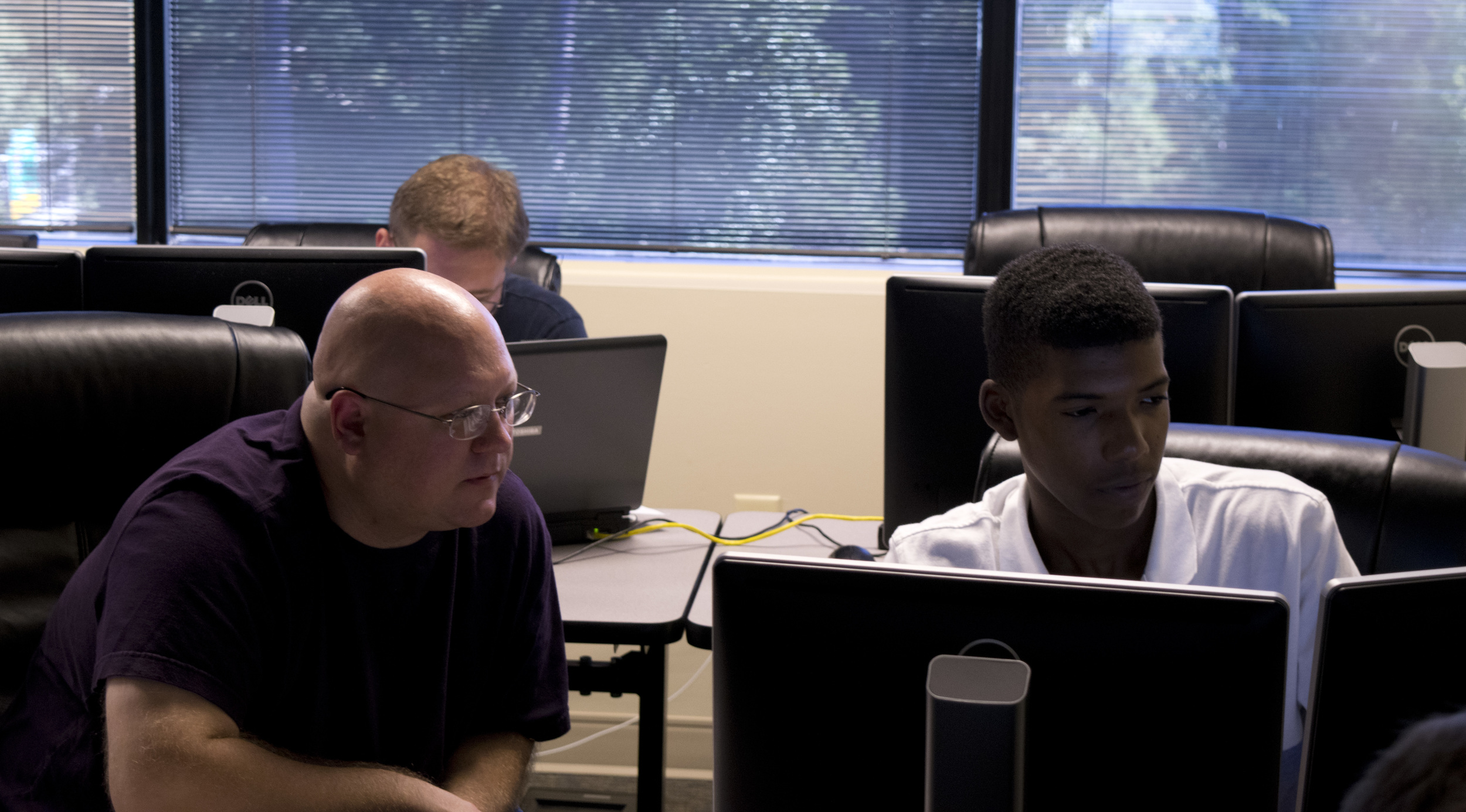
My talk Blue Team Starter Kit presents several security challenges with low cost solutions. It is for security professionals with limited resources including time, money, and people.
LIMITED RESOURCES IS ONLY AN EXCUSE
Limited resources can be it’s own challenge.
“If only we could buy this appliance, all our problems would be solve.”
Except that when that appliance come in, it takes time to configure and train. Oh, and that function that the salesmen says would solve all our problems, ya, that doesn’t work. Some appliances work great. Other times not so great. Unfortunately, when the not so great happens we lose money and time. Look in house before even beginning to research solutions that can solve problems.
Often, I’ve found that appliances are not configured correctly or fully implemented. A little tender, love, and care (TLC) can get appliances running more efficiently and potentially help solve certain challenges. After looking in-house, if the problem still isn't solved, fire up the browser and start researching solutions.
Here are some of the challenges I've had to deal with in the past and the low cost solutions that helped meet those challenges.
Google is a fantastic tool for doing research. It is the first stop to begin solving difficult challenges. Understanding Google’s search techniques is a vital in becoming a proficient IT professional. COST: Behavioural data
So, how do I keep up with information security and it’s every changing ways? How do I keep my thumb on the pulse of the industry? Might I suggest social media and more precisely Twitter. The platform is a wonderful tool for the latest news and tools in information security. It also acts as a forum to interact with people to ask questions and make connections. Sure there is drama, but that can be tuned out (like any appliance). Don’t overlook this as a tool for your security team. I have found a lot of benefit using this in my day-to-day job. COST: Behavioural data
Management approached me with the challenge of doing security assessments on all new applications. With the help of Google, I found a non-profit organization called the Open Web Application Security Project (OWASP). OWASP is an open source community. Within the community is a vast amount of resources to help with application security. This is where I discovered a wonderful tool called the Zed Attack Proxy (ZAP). Setup as a proxy ZAP can be a powerful tool to help security professionals and developers find vulnerabilities in applications. COST: Free
An alternative to this tool is Burp Suite which has a community version and a paid version. COST: $300 year (Professional version)
As part of my job I respond to alerts from the state's Security Operations Center (SOC). Initially, we were just re-imaging the machines. At some point we decided we wanted to get a better understanding of how machines were being infected. I can't remember exactly where I found Redline from Mandiant (now FireEye), but it's helped with meeting this challenge. The tool (largely memory based) collects browsing history, registry and file changes and much more. It then puts it all in one location for automatic and manual analysis. COST:Free
An alternative to this tool is Volatility. COST: Free
Microsoft’s Enhanced Mitigation Experienced Toolkit (EMET) adds an extra layer of protection to machines with Adobe Flash, Java, and Microsoft products involved. Sure, all the Windows XP machines should be off the network, but damn those legacy applications. Worried about that latest Internet Explorer vulnerability? Articles reporting on new vulnerabilities often times have the sentence "EMET mitigates this vulnerability." Like this one. COST: Free
This is a big one and one that might be the most difficult of all the challenges. I tried a couple internal applications (it's amazing how many solutions have a deploy software function), with frustrating results. That is until the sysadmin I worked with suggested Admin Arsenal’s PDQ Deploy. It is a software deployment application that just works. Combined with PDQ Inventory it has the potential to help patch third-party software. COST: $500 (Enterprise version)
CONCLUSION
The challenges and tools above I plan to dive deeper into over the coming weeks. Working with limited resources can be tough and frustrating, but there are solutions. Look internally at existing solutions, first. Then look at external options. There are plenty of expensive appliances out there that will solve the problem. When those are determined to be outside of the budget, start looking at some of the inexpensive options. Often there are simpler and cheaper solutions to challenges. It might take a little more research, but they have the potential to do just as good of a job.
Feedback and suggestions are welcome in the comment section or by email: timothy.deblock[at]gmail[dot]com.